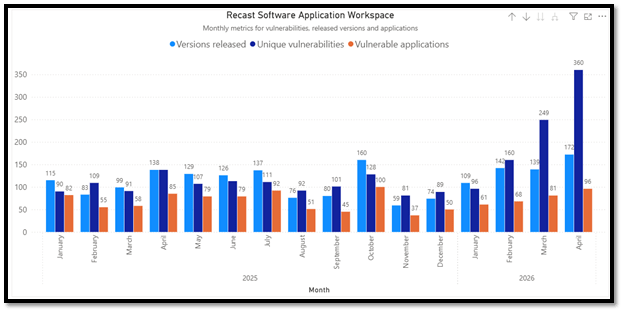
This April was the most active month observed so far in terms of third‑party vulnerability disclosures and remediation activity. During the month, 360 unique vulnerabilities were identified across 96 applications, with vendors releasing 172 patched versions to address these issues. Compared to earlier months, April represents a clear peak in both vulnerability volume and patch output, continuing and amplifying the upward trend seen earlier in the year.
The high vulnerability count in April is primarily driven by a small number of widely deployed products receiving very large security‑focused updates, where a single version remediated dozens of vulnerabilities. As shown in the data in the bottom of this blog, multiple browser releases addressed between 60 and 64 vulnerabilities in one update, including Microsoft Edge (Beta and Business), Google Chrome (standard, Business, and Education builds), Brave Browser, and Vivaldi. Mozilla products also contributed significantly, with Firefox 150.0 remediating 41 vulnerabilities and Thunderbird 150.0 addressing 40 vulnerabilities in single releases.
Notable vulnerabilities in April 2026 third-party patches
Several vulnerabilities disclosed and patched in April 2026 stand out due to confirmed exploit availability and widespread product exposure. In particular, CVE–2026–34621, CVE-2026-5281, and CVE–2025–6965 merit additional attention, as all three have either been actively exploited in the wild or have publicly available proof‑of‑concept exploits. Their inclusion in high‑impact products and libraries significantly shortens the safe remediation window for affected organizations.
CVE–2026–34621 is a high‑severity vulnerability in Adobe Acrobat and Acrobat Reader caused by improper handling of JavaScript object prototype attributes, leading to a prototype pollution condition. Successful exploitation allows arbitrary code execution in the context of the current user when a victim opens a specially crafted malicious PDF file. Adobe has confirmed that this vulnerability was actively exploited in the wild prior to patch availability, and it has been added to CISA’s Known Exploited Vulnerabilities (KEV) catalog. While exploitation requires user interaction, Acrobat and Reader’s broad deployment across enterprise and consumer environments makes this vulnerability particularly impactful. Additional details and fixed versions are documented in Adobe’s official security bulletin and release notes, with KEV status published by CISA.
CVE–2026–5281 is a high‑severity use‑after‑free vulnerability in Google Chrome’s Dawn component, which implements WebGPU functionality. The flaw can be triggered via a crafted HTML page once an attacker has compromised the browser’s renderer process, enabling arbitrary code execution within the browser context. Google has confirmed that an exploit for this vulnerability exists in the wild, and it was added to CISA’s Known Exploited Vulnerabilities (KEV) catalog on April 1, 2026, classifying it as a zero‑day at the time of disclosure. Due to Chromium’s shared codebase, this vulnerability also affects other Chromium‑based browsers such as Microsoft Edge, Brave, and Vivaldi until patched downstream. Organizations should treat this issue as high‑priority and ensure all Chromium‑based browsers are fully up to date.
CVE–2025-6965 is a critical memory corruption vulnerability in SQLite, caused by improper handling of aggregate terms exceeding available columns. This vulnerability was published on July 15, 2025. It was originally discovered by Google’s Big Sleep. The vulnerability resurfaced in this blog because it seems that it was only now patched in Microsoft Visual Studio. Under certain conditions, this flaw can result in out-of-bounds memory access, potentially leading to crashes or arbitrary code execution.
Browser security updates in April 2026
Browser updates were a major contributor to April’s vulnerability volume, with several browsers receiving multiple releases remediating large numbers of vulnerabilities per version. Chromium‑based browsers in particular account for the highest counts, driven by upstream Chromium security fixes that propagate across multiple vendors and distribution channels. Mozilla browsers also shipped large security updates, including both standard and ESR releases.
| Browser | Vulnerabilities | Updates |
| Google Chrome | 121 | 3 |
| Microsoft Edge | 139 | 5 |
| Brave Browser | 176 | 6 |
| Mozilla Firefox | 100 | 6 |
| Mozilla Firefox 115 | 60 | 6 |
| Mozilla Firefox 140 | 56 | 4 |
| Opera One | 21 | 1 |
| Pale Moon | 5 | 1 |
| Vivaldi | 122 | 4 |
| Waterfox | 25 | 1 |
Microsoft product updates included in April 2026 third-party patches
Microsoft issued security updates for several other products:
- Microsoft .NET Runtime 10.0
- Microsoft .NET Runtime 8.0
- Microsoft .NET Runtime 9.0
- Microsoft .NET SDK 10.0
- Microsoft .NET SDK 8.0
- Microsoft .NET SDK 9.0
- Microsoft 365 Apps
- Microsoft ASP.NET Core Runtime 10.0
- Microsoft ASP.NET Core Runtime 8.0
- Microsoft ASP.NET Core Runtime 9.0
- Microsoft ASP.NET Core Runtime Hosting Bundle 10.0
- Microsoft ASP.NET Core Runtime Hosting Bundle 8.0
- Microsoft ASP.NET Core Runtime Hosting Bundle 9.0
- Microsoft Azure CLI
- Microsoft Edge Beta
- Microsoft Edge for Business
- Microsoft Project
- Microsoft Visio
- Microsoft Visual Studio 2022 Community
- Microsoft Visual Studio 2022 Enterprise
- Microsoft Visual Studio 2022 Professional
- Microsoft Visual Studio Code
- Microsoft Visual Studio Team Explorer 2022
- Microsoft Windows Desktop Runtime 10.0
- Microsoft Windows Desktop Runtime 8.0
- Microsoft Windows Desktop Runtime 9.0
Detailed list of April third-party patches
| ProductName | Version Name | Vulnerabilities remediated |
| Adobe Acrobat DC | 26.001.21431 | 2 |
| Adobe Acrobat DC | 26.001.21411 | 1 |
| Adobe Acrobat Reader DC | 26.001.21431 | 2 |
| Adobe Acrobat Reader DC | 26.001.21411 | 1 |
| Adobe Acrobat Reader DC – Multilingual (MUI) | 26.001.21431 | 2 |
| Adobe Acrobat Reader DC – Multilingual (MUI) | 26.001.21411 | 1 |
| Amazon Corretto JDK | 25.0.3.9.1 | 9 |
| Amazon Corretto JDK | 26.0.1.8.1 | 9 |
| Amazon Corretto JDK 11 | 11.0.31.11.1 | 8 |
| Amazon Corretto JDK 17 | 17.0.19.10.1 | 8 |
| Amazon Corretto JDK 21 | 21.0.11.10.1 | 8 |
| Amazon Corretto JDK 8 | 8.492.09.1 | 7 |
| Amazon Corretto JRE 8 | 8.492.09.1 | 7 |
| Amazon SSM Agent | 3.3.4121.0 | 1 |
| Apache Tomcat 10 | 10.1.54 | 4 |
| Apache Tomcat 11 | 11.0.21 | 4 |
| Apache Tomcat 9 | 9.0.117 | 4 |
| Brave Browser | 1.89.132 | 60 |
| Brave Browser | 1.89.141 | 31 |
| Brave Browser | 1.89.137 | 31 |
| Brave Browser | 1.89.145 | 30 |
| Brave Browser | 1.88.138 | 21 |
| Brave Browser | 1.89.143 | 3 |
| Burp Suite Community Edition | 2026.3.2 | 21 |
| Burp Suite Professional Edition | 2026.3.2 | 21 |
| Electron | 39.8.9 | 27 |
| Electron | 40.9.2 | 26 |
| Electron | 41.2.2 | 25 |
| Erlang OTP | 28.4.2.0 | 3 |
| Erlang OTP | 28.4.3.0 | 1 |
| Foxit PDF Editor | 2026.1.1.36485 | 7 |
| Foxit PDF Editor | 2026.1.0.36452 | 7 |
| Foxit PDF Editor | 2026.1.0.70169 | 4 |
| Foxit PDF Editor 13 | 13.2.4.24048 | 5 |
| Foxit PDF Editor Pro 13 | 13.2.4.24048 | 5 |
| Foxit PDF Reader | 2026.1.1.36485 | 7 |
| Foxit PDF Reader | 2026.1.0.36452 | 7 |
| Foxit PDF Reader | 2026.1.0.36452 | 4 |
| Git | 2.53.0 | 2 |
| Git | 2.53.0.3 | 2 |
| Google Chrome | 147.0.7727.56 | 60 |
| Google Chrome | 147.0.7727.101 | 31 |
| Google Chrome | 147.0.7727.102 | 31 |
| Google Chrome | 147.0.7727.137 | 30 |
| Google Chrome | 147.0.7727.138 | 30 |
| Google Chrome | 147.0.7727.116 | 3 |
| Google Chrome for Business | 147.0.7727.56 | 60 |
| Google Chrome for Business | 147.0.7727.102 | 31 |
| Google Chrome for Business | 147.0.7727.138 | 30 |
| Google Chrome for Education | 147.0.7727.56 | 60 |
| Google Chrome for Education | 147.0.7727.102 | 31 |
| Google Chrome for Education | 147.0.7727.138 | 30 |
| Google Go Programming Language | 1.26.2 | 10 |
| Google Go Programming Language | 1.25.9 | 10 |
| Greenshot | 1.3.315 | 1 |
| Helm | 4.1.4 | 3 |
| ImageMagick | 7.1.2.19 | 12 |
| ImageMagick | 7.1.2.21 | 1 |
| IntelliJ IDEA | 2025.3.4.1 | 1 |
| IntelliJ IDEA Community | 2025.1.7.1 | 1 |
| IntelliJ IDEA Community | 2024.3.7.1 | 1 |
| IntelliJ IDEA Community | 2025.2.6.2 | 1 |
| IntelliJ IDEA Ultimate | 2024.3.7.1 | 1 |
| Liberica JDK | 25.0.3.11 | 10 |
| Liberica JDK | 11.0.31.11 | 9 |
| Liberica JDK | 17.0.19.11 | 9 |
| Liberica JDK | 8.0.492.9 | 8 |
| Liberica JDK Lite | 25.0.3.11 | 10 |
| Liberica JDK Lite | 21.0.11.11 | 9 |
| Liberica JDK Lite | 11.0.31.11 | 9 |
| Liberica JDK Lite | 8.0.492.9 | 8 |
| Liberica JRE | 25.0.3.11 | 10 |
| Liberica JRE | 21.0.11.11 | 9 |
| Liberica JRE | 11.0.31.11 | 9 |
| Liberica JRE | 8.0.492.9 | 8 |
| Microsoft .NET Runtime 10.0 | 10.0.6 | 4 |
| Microsoft .NET Runtime 10.0 | 10.0.7 | 1 |
| Microsoft .NET Runtime 8.0 | 8.0.26 | 4 |
| Microsoft .NET Runtime 8.0 | 8.0.26.35919 | 4 |
| Microsoft .NET Runtime 9.0 | 9.0.15 | 4 |
| Microsoft .NET SDK 10.0 | 10.0.202 | 4 |
| Microsoft .NET SDK 10.0 | 10.0.203 | 1 |
| Microsoft .NET SDK 8.0 | 8.4.2026.17201 | 4 |
| Microsoft .NET SDK 8.0 | 8.0.420 | 4 |
| Microsoft .NET SDK 9.0 | 9.0.313 | 4 |
| Microsoft 365 Apps | 2603 (Build 16.0.19822.20182) | 12 |
| Microsoft 365 Apps | 2603 (Build 16.0.19822.20180) | 12 |
| Microsoft 365 Apps | 2508 (Build 16.0.19127.20622) | 12 |
| Microsoft ASP.NET Core Runtime 10.0 | 10.0.6 | 4 |
| Microsoft ASP.NET Core Runtime 10.0 | 10.0.7 | 1 |
| Microsoft ASP.NET Core Runtime 8.0 | 8.0.26 | 4 |
| Microsoft ASP.NET Core Runtime 8.0 | 8.0.26.26169 | 4 |
| Microsoft ASP.NET Core Runtime 9.0 | 9.0.15 | 4 |
| Microsoft ASP.NET Core Runtime Hosting Bundle 10.0 | 10.0.6 | 4 |
| Microsoft ASP.NET Core Runtime Hosting Bundle 10.0 | 10.0.7 | 1 |
| Microsoft ASP.NET Core Runtime Hosting Bundle 8.0 | 8.0.26.26169 | 4 |
| Microsoft ASP.NET Core Runtime Hosting Bundle 9.0 | 9.0.15 | 4 |
| Microsoft Azure CLI | 2.85.0 | 6 |
| Microsoft Edge Beta | 147.0.3912.60 | 64 |
| Microsoft Edge for Business | 147.0.3912.60 | 64 |
| Microsoft Edge for Business | 147.0.3912.72 | 28 |
| Microsoft Edge for Business | 147.0.3912.98 | 27 |
| Microsoft Edge for Business | 146.0.3856.97 | 18 |
| Microsoft Edge for Business | 147.0.3912.86 | 2 |
| Microsoft Project | 2603 (Build 16.0.19822.20182) | 12 |
| Microsoft Remote Desktop | 1.2.7099.0 | 1 |
| Microsoft Visio | 2603 (Build 16.0.19822.20182) | 12 |
| Microsoft Visual Studio 2019 Enterprise | 16.11.37206.5 | 3 |
| Microsoft Visual Studio 2019 Professional | 16.11.37206.5 | 3 |
| Microsoft Visual Studio 2022 Enterprise | 17.12.37202.15 | 5 |
| Microsoft Visual Studio 2022 Enterprise | 17.14.37203.1 | 5 |
| Microsoft Visual Studio 2022 Professional | 17.12.37202.15 | 5 |
| Microsoft Visual Studio 2022 Professional | 17.14.37203.1 | 5 |
| Microsoft Windows Desktop Runtime 10.0 | 10.0.6 | 4 |
| Microsoft Windows Desktop Runtime 10.0 | 10.0.7 | 1 |
| Microsoft Windows Desktop Runtime 8.0 | 8.0.26.35920 | 4 |
| Microsoft Windows Desktop Runtime 9.0 | 9.0.15 | 4 |
| Mozilla Firefox | 150.0 | 41 |
| Mozilla Firefox | 149.0.2 | 5 |
| Mozilla Firefox | 150.0.1 | 4 |
| Mozilla Firefox ESR 115 | 115.35.0 | 25 |
| Mozilla Firefox ESR 115 | 115.35.1 | 4 |
| Mozilla Firefox ESR 115 | 115.34.1 | 1 |
| Mozilla Firefox ESR 140 | 140.10.0 | 25 |
| Mozilla Firefox ESR 140 | 140.10.1 | 4 |
| Mozilla Firefox ESR 140 | 140.9.1 | 3 |
| Mozilla Thunderbird | 150.0 | 40 |
| Mozilla Thunderbird | 149.0.2 | 10 |
| Mozilla Thunderbird | 149.0.2 | 5 |
| Mozilla Thunderbird ESR 140 | 140.10.0 | 25 |
| Mozilla Thunderbird ESR 140 | 140.9.1 | 6 |
| Mozilla Thunderbird ESR 140 | 140.9.1 | 3 |
| Notepad++ | 8.9.4 | 2 |
| OpenSSL | 3.6.2 | 8 |
| OpenSSL | 3.5.6 | 7 |
| OpenSSL | 3.0.20 | 6 |
| OpenSSL | 3.3.7 | 6 |
| OpenSSL | 3.4.5 | 6 |
| OpenSSL Light | 3.6.2 | 8 |
| OpenSSL Light | 3.5.6 | 7 |
| OpenSSL Light | 3.4.5 | 6 |
| OpenSSL Light | 3.3.7 | 6 |
| OpenSSL Light | 3.0.20 | 6 |
| Opera One | 130.0.5847.12 | 21 |
| Oracle Java Runtime Environment Version 8 | 8.0.4910.10 | 7 |
| Oracle Java SE Development Kit | 25.0.3.0 | 8 |
| Oracle Java SE Development Kit 21 | 21.0.11.0 | 8 |
| Oracle Java SE Development Kit 8 | 8.0.4910.10 | 7 |
| Pale Moon | 34.2.0 | 5 |
| Prometheus | 3.11.3 | 2 |
| Prometheus | 3.11.2 | 1 |
| Python 3.13 | 3.13.13 | 3 |
| Python 3.14 | 3.14.4 | 3 |
| Rocket.Chat | 4.14.0 | 1 |
| Splunk Enterprise | 10.2.2 | 2 |
| Splunk Enterprise | 10.0.5 | 2 |
| Splunk Enterprise 9.3 | 9.3.11 | 2 |
| Splunk Enterprise 9.4 | 9.4.10 | 2 |
| Splunk Universal Forwarder 9.3 | 9.3.11 | 1 |
| Splunk Universal Forwarder 9.4 | 9.4.10 | 1 |
| Vivaldi | 7.9.3970.50 | 60 |
| Vivaldi | 7.9.3970.55 | 31 |
| Vivaldi | 7.9.3970.60 | 30 |
| Vivaldi | 7.9.3970.47 | 1 |
| Waterfox | 6.6.12 | 25 |
| Wireshark | 4.6.5 | 41 |
| Wireshark | 4.4.15 | 36 |
| Zulu JDK 11 (LTS) | 11.88.17 | 8 |
| Zulu JDK 17 (LTS) | 17.66.19 | 8 |
| Zulu JDK 21 (LTS) | 21.50.19 | 8 |
| Zulu JDK 25 (LTS) | 25.34.17.0 | 9 |
| Zulu JRE 11 (LTS) | 11.88.17 | 8 |
| Zulu JRE 17 (LTS) | 17.66.19 | 8 |
| Zulu JRE 21 (LTS) | 21.50.19 | 8 |
| Zulu JRE 25 (LTS) | 25.34.17.0 | 9 |
Application management at the speed of your operations
Vulnerabilities move fast, especially in a distributed workforce. Discover how Recast’s application management product, Application Workspace, helps IT teams keep applications patched, compliant, and correctly configured, wherever work happens.


