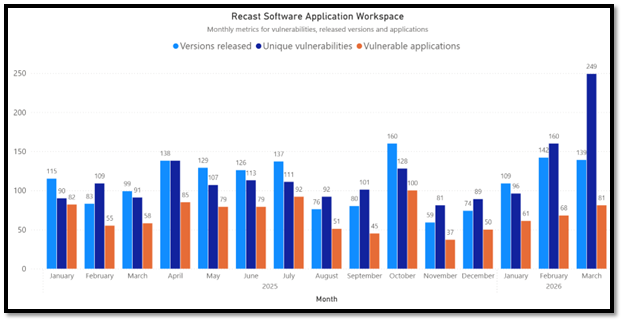
March marked a clear increase in vulnerability and remediation activity compared to February. We identified 249 unique vulnerabilities affecting 81 applications, and remediation work resulted in 139 unique updates during the month. Both the volume of findings and patching activity rose notably, making March one of the more active periods so far this year.
Last month stands out due to the volume of vulnerabilities remediated, but this is largely explained by how vendors released patches during that time. Several major products shipped bulk security updates, where a single version fixed dozens of vulnerabilities at once. Browsers and runtimes in particular accounted for much of the increase, as they routinely bundle large numbers of memory‑safety fixes into scheduled releases.
Notable vulnerabilities in March 2026 third-party patches
CVE-2026-5281, CVE‑2026‑3910, and CVE‑2026‑3909 all stand out this month due to the availability of public exploits. While not all environments will be directly exposed, the existence of working exploits significantly increases the risk of real‑world abuse and shortens the time window for safe remediation.
CVE-2026-5281 is a high‑severity vulnerability in Google Chrome’s Dawn component, which implements WebGPU functionality. The flaw is a use‑after‑free condition that can be triggered after an attacker has already compromised the browser’s renderer process. By abusing this memory‑safety issue through a specially crafted HTML page, an attacker can achieve arbitrary code execution within the context of the browser. Google confirmed that this vulnerability was actively exploited in the wild prior to the availability of a patch. It has been added to CISA’s Known Exploited Vulnerabilities (KEV) catalog. The assigned CVSS 3 score of 8.8 (High) reflects both the technical impact and the realistic exploitation potential when combined with other browser flaws. More information is available in the Chrome Releases security advisory and CISA’s KEV entry.
CVE‑2026‑3910 affects Google Chrome’s V8 JavaScript engine and is caused by an inappropriate implementation that can be abused through a specially crafted HTML page. The flaw allows a remote attacker to execute arbitrary code inside the browser’s sandbox, without requiring authentication or direct user interaction beyond visiting a malicious webpage. This isn’t the first time V8 has had a zero-day vulnerability. Google has confirmed that CVE‑2026‑3910 has been actively exploited in the wild, and the vulnerability is listed in CISA’s Known Exploited Vulnerabilities (KEV) catalog. As with other V8 vulnerabilities, Chromium‑based browsers that lag behind Chrome’s patch cadence may also be affected. Organizations should prioritize updating Chrome and other Chromium‑based browsers to patched versions, particularly in environments where users routinely browse untrusted or external web content. Additional technical details and remediation guidance are available through Chrome Releases and CISA KEV.
CVE–2026–3909 is a high‑severity vulnerability in Google Skia, an open‑source 2D graphics library used by Google Chrome and a broad range of other platforms, including ChromeOS, Android, Flutter, and additional Chromium‑based products. The vulnerability is an out‑of‑bounds write, triggered via a crafted HTML page, which allows a remote attacker to perform out‑of‑bounds memory access. The vulnerability was actively exploited in the wild prior to patch availability, and it has been added to CISA’s Known Exploited Vulnerabilities (KEV) catalog. The issue affects Google Chrome versions prior to 146.0.7680.75, but due to Skia’s widespread use, the potential impact extends beyond Chrome itself. Products embedding Skia or relying on Chromium components may also be affected depending on how quickly upstream patches were integrated. More information can be found on Chrome Releases security advisory and CISA KEV.
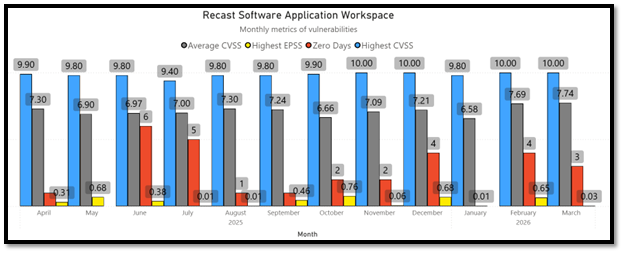
March also saw several vulnerabilities assigned the maximum CVSS score of 10, indicating critical severity and the potential for full compromise of affected systems if exploited. CVE-2026-4689, CVE-2026-4725 and CVE–2026–4692 impact Mozilla Firefox and Thunderbird, where flaws in boundary handling can lead to sandbox escape scenarios, allowing malicious code to break out of browser isolation. CVE–2026–4688 also affects Firefox through a use‑after‑free condition in the Disability Access APIs, which could enable elevated impact under specific conditions.
CVE‑2025‑68121 is a critical vulnerability in the Go programming language’s crypto/tls library. Any Go‑based software that uses the affected TLS functionality may be impacted. This includes Microsoft Azure Kubelogin, which relies on Go’s TLS implementation to authenticate and integrate Azure identity with Kubernetes clusters.
Browser security updates in March 2026
Major browsers, including Google Chrome, Microsoft Edge, Brave, Mozilla Firefox (including ESR versions), Opera One, Vivaldi, and others received numerous security updates addressing various vulnerabilities.
| Browser | Vulnerabilities | Updates |
| Google Chrome | 87 | 6 |
| Microsoft Edge | 41 | 4 |
| Brave Browser | 74 | 5 |
| Mozilla Firefox | 49 | 2 |
| Mozilla Firefox 115 | 17 | 1 |
| Mozilla Firefox 140 | 38 | 2 |
| Pale Moon | 8 | 1 |
| Vivaldi | 2 | 1 |
| Waterfox | 38 | 1 |
Microsoft product updates included in March 2026 third-party patches
Microsoft issued security updates for several other products:
- Microsoft .NET Runtime 10.0
- Microsoft .NET Runtime 8.0
- Microsoft .NET Runtime 9.0
- Microsoft .NET SDK 10.0
- Microsoft .NET SDK 8.0
- Microsoft .NET SDK 9.0
- Microsoft 365 Apps
- Microsoft ASP.NET Core Runtime 10.0
- Microsoft ASP.NET Core Runtime 8.0
- Microsoft ASP.NET Core Runtime 9.0
- Microsoft ASP.NET Core Runtime Hosting Bundle 10.0
- Microsoft ASP.NET Core Runtime Hosting Bundle 8.0
- Microsoft ASP.NET Core Runtime Hosting Bundle 9.0
- Microsoft Azure CLI
- Microsoft Edge Beta
- Microsoft Edge for Business
- Microsoft Project
- Microsoft Visio
- Microsoft Visual Studio 2022 Community
- Microsoft Visual Studio 2022 Enterprise
- Microsoft Visual Studio 2022 Professional
- Microsoft Visual Studio Code
- Microsoft Visual Studio Team Explorer 2022
- Microsoft Windows Desktop Runtime 10.0
- Microsoft Windows Desktop Runtime 8.0
- Microsoft Windows Desktop Runtime 9.0
Detailed list of March 2026 third-party patches
For a complete list of applications, versions, and the number of remediated vulnerabilities, see the table below generated using Application Workspace data.
| ProductName | Version Name | Vulnerabilities remediated |
| Accessibility Insights for Windows | 1.1.2924.1 | 1 |
| Adobe Acrobat DC | 25.001.21288 | 3 |
| Adobe Acrobat Reader DC | 25.001.21288 | 3 |
| Adobe Acrobat Reader DC – Multilingual (MUI) | 25.001.21288 | 3 |
| Application Workspace Agent 4 | 4.4.4174.8323 | 1 |
| Autodesk Revit 2023 | Temp 03/06/2026 07:46:37 2023.1.9 | 1 |
| Brave Browser | 1.88.136 | 8 |
| Brave Browser | 1.88.134 | 26 |
| Brave Browser | 1.87.192 | 10 |
| Brave Browser | 1.88.127 | 29 |
| Brave Browser | 1.88.132 | 1 |
| Burp Suite Community Edition | 2026.3.1 | 26 |
| Burp Suite Community Edition | 2026.2.3 | 11 |
| Burp Suite Professional Edition | 2026.3.1 | 26 |
| Burp Suite Professional Edition | 2026.2.3 | 11 |
| ClamAV | 1.5.2 | 1 |
| Cryptomator | 1.19.2 | 1 |
| Cryptomator | 1.19.2.6322 | 1 |
| Cryptomator | 1.19.1 | 3 |
| Cryptomator | 1.19.1.6316 | 3 |
| Datadog Agent | 7.76.3 | 1 |
| Docker Desktop | 4.67.0 | 1 |
| Docker Desktop | 4.67.0.222858 | 1 |
| Erlang OTP | 28.4.1.0 | 3 |
| Foxit PDF Editor 13 | 13.2.3.24041 | 4 |
| Foxit PDF Editor Pro 13 | 13.2.3.24041 | 4 |
| Git | 2.53.0.2 | 1 |
| Google Chrome | 146.0.7680.178 | 21 |
| Google Chrome | 146.0.7680.177 | 21 |
| Google Chrome | 146.0.7680.164 | 8 |
| Google Chrome | 146.0.7680.165 | 8 |
| Google Chrome | 145.0.7632.159 | 10 |
| Google Chrome | 146.0.7680.75 | 2 |
| Google Chrome | 146.0.7680.76 | 2 |
| Google Chrome | 146.0.7680.153 | 26 |
| Google Chrome | 146.0.7680.154 | 26 |
| Google Chrome | 146.0.7680.80 | 1 |
| Google Chrome | 146.0.7680.71 | 29 |
| Google Chrome | 146.0.7680.72 | 29 |
| Google Chrome for Business | 146.0.7680.178 | 21 |
| Google Chrome for Business | 146.0.7680.154 | 26 |
| Google Chrome for Business | 146.0.7680.165 | 8 |
| Google Chrome for Business | 146.0.7680.76 | 2 |
| Google Chrome for Business | 146.0.7680.80 | 1 |
| Google Chrome for Business | 146.0.7680.72 | 29 |
| Google Chrome for Education | 146.0.7680.178 | 21 |
| Google Chrome for Education | 146.0.7680.154 | 26 |
| Google Chrome for Education | 146.0.7680.165 | 8 |
| Google Chrome for Education | 146.0.7680.76 | 2 |
| Google Chrome for Education | 146.0.7680.80 | 1 |
| Google Chrome for Education | 146.0.7680.72 | 29 |
| Google Go Programming Language | 1.26.1 | 5 |
| Google Go Programming Language | 1.25.8 | 5 |
| Grafana k6 | 1.7.1 | 1 |
| IBM Semeru Runtime Open Edition JDK 8 (LTS) | 8.0.482.8 | 5 |
| IBM Semeru Runtime Open Edition JRE 8 (LTS) | 8.0.482.8 | 5 |
| Microsoft .NET Runtime 10.0 | 10.0.4 | 3 |
| Microsoft .NET Runtime 8.0 | 8.0.25 | 1 |
| Microsoft .NET Runtime 8.0 | 8.0.25.35812 | 1 |
| Microsoft .NET Runtime 9.0 | 9.0.14 | 2 |
| Microsoft .NET SDK 10.0 | 10.0.200 | 3 |
| Microsoft .NET SDK 8.0 | 8.0.419 | 1 |
| Microsoft .NET SDK 8.0 | 8.4.1926.11301 | 1 |
| Microsoft .NET SDK 9.0 | 9.0.312 | 2 |
| Microsoft 365 Apps | 2602 (Build 16.0.19725.20170) | 7 |
| Microsoft 365 Apps | 2508 (Build 16.0.19127.20570) | 7 |
| Microsoft 365 Apps | 2602 (Build 16.0.19725.20172) | 7 |
| Microsoft ASP.NET Core Runtime 10.0 | 10.0.4 | 3 |
| Microsoft ASP.NET Core Runtime 8.0 | 8.0.25 | 1 |
| Microsoft ASP.NET Core Runtime 8.0 | 8.0.25.26112 | 1 |
| Microsoft ASP.NET Core Runtime 9.0 | 9.0.14 | 2 |
| Microsoft ASP.NET Core Runtime Hosting Bundle 10.0 | 10.0.4 | 3 |
| Microsoft ASP.NET Core Runtime Hosting Bundle 8.0 | 8.0.25.26112 | 1 |
| Microsoft ASP.NET Core Runtime Hosting Bundle 9.0 | 9.0.14 | 2 |
| Microsoft Azure Kubelogin | 0.2.16 | 4 |
| Microsoft Edge Beta | 146.0.3856.59 | 31 |
| Microsoft Edge Beta | 146.0.3856.62 | 1 |
| Microsoft Edge for Business | 146.0.3856.84 | 9 |
| Microsoft Edge for Business | 146.0.3856.72 | 23 |
| Microsoft Edge for Business | 146.0.3856.72 | 24 |
| Microsoft Edge for Business | 146.0.3856.72 | 22 |
| Microsoft Edge for Business | 145.0.3800.97 | 9 |
| Microsoft Edge for Business | 146.0.3856.59 | 34 |
| Microsoft Edge for Business | 146.0.3856.62 | 1 |
| Microsoft Project | 2602 (Build 16.0.19725.20172) | 7 |
| Microsoft Visio | 2602 (Build 16.0.19725.20172) | 7 |
| Microsoft Visual Studio 2019 Enterprise | 16.11.37027.11 | 1 |
| Microsoft Visual Studio 2019 Professional | 16.11.37027.11 | 1 |
| Microsoft Visual Studio 2022 Enterprise | 17.14.37027.9 | 3 |
| Microsoft Visual Studio 2022 Enterprise | 17.12.37027.10 | 3 |
| Microsoft Visual Studio 2022 Professional | 17.14.37027.9 | 3 |
| Microsoft Visual Studio 2022 Professional | 17.12.37027.10 | 3 |
| Microsoft Visual Studio Tools for Applications | 17.1.37110.0 | 1 |
| Microsoft Windows Desktop Runtime 10.0 | 10.0.4 | 3 |
| Microsoft Windows Desktop Runtime 8.0 | 8.0.25.35812 | 1 |
| Microsoft Windows Desktop Runtime 9.0 | 9.0.14 | 2 |
| MongoDB Community Edition 8.2 | 8.2.6 | 2 |
| MongoDB Enterprise Edition 8.2 | 8.2.6 | 2 |
| Mozilla Firefox | 149.0 | 46 |
| Mozilla Firefox | 149.0 | 41 |
| Mozilla Firefox | 148.0.2 | 3 |
| Mozilla Firefox ESR 115 | 115.34.0 | 17 |
| Mozilla Firefox ESR 140 | 140.9.0 | 38 |
| Mozilla Firefox ESR 140 | 140.9.0 | 12 |
| Mozilla Thunderbird | 149.0 | 48 |
| Mozilla Thunderbird | 149.0 | 44 |
| Mozilla Thunderbird ESR 140 | 140.9.0 | 40 |
| Mozilla Thunderbird ESR 140 | 140.9.0 | 34 |
| nginx | 1.29.7 | 6 |
| nginx | 1.28.3 | 6 |
| nginx | 1.29.5 | 1 |
| nginx | 1.28.2 | 1 |
| Node.js 20 LTS | 20.20.2 | 7 |
| Node.js 22 LTS | 22.22.2 | 7 |
| Node.js 24 | 24.14.1 | 8 |
| Node.js 25 | 25.8.2 | 9 |
| NoMachine | 9.4.14 | 1 |
| NoMachine Enterprise Client | 9.4.14 | 1 |
| NoMachine Enterprise Desktop | 9.4.14 | 1 |
| NoMachine Fonts 100dpi | 9.4.14 | 1 |
| NoMachine Fonts 75dpi | 9.4.14 | 1 |
| NoMachine Fonts Misc | 9.4.14 | 1 |
| NoMachine Fonts Others | 9.4.14 | 1 |
| Notepad++ | 8.9.3 | 1 |
| Opera One | 129.0.5823.15 | 5 |
| Pale Moon | 34.1.0 | 16 |
| Pale Moon | 34.1.0 | 8 |
| PaperCut MF | 25.0.10.75465 | 1 |
| PaperCut NG | 25.0.10.75466 | 1 |
| Sandboxie Classic | 5.72.3 | 1 |
| Sandboxie Plus | 1.17.3 | 1 |
| Splunk Enterprise | 10.2.1 | 7 |
| Splunk Enterprise | 10.0.4 | 7 |
| Splunk Enterprise 9.3 | 9.3.10 | 7 |
| Splunk Enterprise 9.4 | 9.4.9 | 7 |
| Vivaldi | 7.8.3925.79 | 2 |
| Vivaldi | 7.8.3925.81 | 2 |
| Waterfox | 6.6.10 | 38 |
Application management at the speed of your operations
Vulnerabilities move fast, especially in a distributed workforce. Discover how Recast’s application management product, Application Workspace, helps IT teams keep applications patched, compliant, and correctly configured, wherever work happens.
