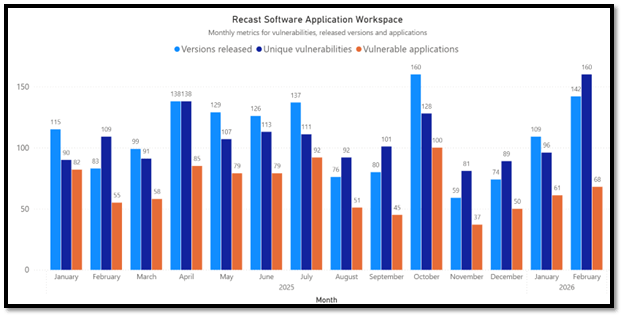
February saw a clear jump in activity compared to January. We tracked 160 unique vulnerabilities across 68 applications, and remediation efforts resulted in 142 version updates. Both findings and patch volume increased notably month over month, making February one of the more active periods since last October.
Notable vulnerabilities in February 2026 third-party patches
February saw several high‑risk vulnerabilities, but four zero‑day issues clearly stood out and required the most attention.
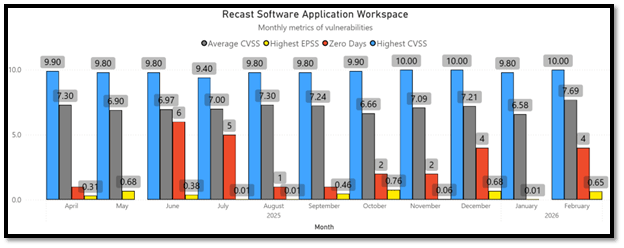
CVE‑2025‑55182 was the most severe, with a CVSS score of 10.0, active exploitation, and a publicly available exploit. Its elevated EPSS score (0.64814) further indicated a high likelihood of real‑world abuse, making it a critical priority. The vulnerability affects React Server Components. The flaw allows an attacker to execute arbitrary code by sending crafted HTTP payloads to exposed React Server Function endpoints, without requiring authentication or user interaction. Due to its CVSS 10.0 severity and remote exploitability, affected applications should be patched immediately following vendor guidance. In addition, public proofs-of-concept (POC) are now widely available, and public security research has identified threat actor exploitation attempts, including reported China-linked threat actors.
The reason why CVE‑2025‑55182 is mentioned in this blog is that not all the vendors had patched the vulnerability even though it was made public March 12, 2025. From the Application Workspace catalog this vulnerability affected Coder by Coder Technologies, Inc. across multiple platforms and package formats. Impacted versions include Coder Mainline on Windows, as well as Coder for Linux (Mainline). More information can be found on GitHub and more generally about the vulnerability on CISA KEV.
CVE–2026–2441 is a high‑severity zero‑day vulnerability affecting Google Chrome, with a CVSS score of 8.8. Google has confirmed that vulnerability was actively exploited in the wild prior to the release of a patch, and that a working exploit exists. The flaw is a use‑after‑free vulnerability in Chrome’s CSS engine, which can be triggered when a user visits a specially crafted malicious webpage. Successful exploitation allows a remote attacker to execute arbitrary code inside the browser’s sandbox, without requiring authentication or additional user interaction beyond visiting the page. More information can be found on Chrome Releases and on CISA KEV.
CVE–2026–21514 is a critical zero‑day vulnerability in Microsoft Word, with a CVSS score of 7.8. Microsoft has confirmed that vulnerability has been actively exploited in the wild. The flaw is categorized as a security feature bypass, caused by Microsoft Word relying on untrusted inputs when making security decisions. This allows attackers to circumvent protections that are intended to warn or block malicious content in Word documents. Exploitation requires user interaction, typically by convincing a victim to open a specially crafted Word document delivered via phishing or other social‑engineering techniques. More information can be found on MSRC and CISA KEV.
CVE–2026–21509 is a another zero‑day in Microsoft Office that stood out this month due to its severity and real‑world exploitation. With a CVSS score of 7.8, the issue has already been abused in active attacks. Exploitation requires social engineering. Victims are persuaded to open a malicious Office document, typically delivered via phishing. Once the file is opened, it can slip past normal security prompts and provide attackers with a foothold for subsequent malicious activity. More information can be found on MSRC and CISA KEV.
Alongside these, several other critical vulnerabilities with high CVSS scores (including multiple browser and platform components) were disclosed during the month. While they are not zero‑days, they remain important and should be addressed promptly through standard patch management processes.
- CVE-2026-2778 (Firefox and Thunderbird)
- CVE-2026-2776 (Firefox and Thunderbird)
- CVE-2026-2768 (Firefox and Thunderbird)
- CVE-2025-68121 (Go Language in GitHub)
- CVE-2026-2760 (Firefox and Thunderbird)
- CVE-2026-2761 (Firefox and Thunderbird)
Browser security updates in February 2026
Major browsers, including Google Chrome, Microsoft Edge, Brave, Mozilla Firefox (including ESR versions), Opera One, Vivaldi, and others received numerous security updates addressing various vulnerabilities.
Firefox shows a higher number of patched vulnerabilities this month, largely due to Mozilla releasing bundled security updates across multiple supported branches, including ESR versions. Many of these fixes address the same underlying issues and reflect Mozilla’s transparent disclosure and long‑term support model rather than increased risk.
| Browser | Vulnerabilities | Updates |
| Google Chrome | 20 | 5 |
| Microsoft Edge | 38 | 6 |
| Brave Browser | 17 | 4 |
| Mozilla Firefox | 52 | 3 |
| Mozilla Firefox 115 | 22 | 2 |
| Mozilla Firefox 140 | 38 | 2 |
| Vivaldi | 4 | 2 |
| Waterfox | 37 | 1 |
Microsoft product updates included in February 2026 third-party patches
Microsoft issued security updates for several other products:
- Microsoft .NET Runtime 10.0
- Microsoft .NET Runtime 8.0
- Microsoft .NET Runtime 9.0
- Microsoft .NET SDK 10.0
- Microsoft .NET SDK 8.0
- Microsoft .NET SDK 9.0
- Microsoft 365 Apps
- Microsoft ASP.NET Core Runtime 10.0
- Microsoft ASP.NET Core Runtime 8.0
- Microsoft ASP.NET Core Runtime 9.0
- Microsoft ASP.NET Core Runtime Hosting Bundle 10.0
- Microsoft ASP.NET Core Runtime Hosting Bundle 8.0
- Microsoft ASP.NET Core Runtime Hosting Bundle 9.0
- Microsoft Azure CLI
- Microsoft Edge Beta
- Microsoft Edge for Business
- Microsoft Project
- Microsoft Visio
- Microsoft Visual Studio 2022 Community
- Microsoft Visual Studio 2022 Enterprise
- Microsoft Visual Studio 2022 Professional
- Microsoft Visual Studio Code
- Microsoft Visual Studio Team Explorer 2022
- Microsoft Windows Desktop Runtime 10.0
- Microsoft Windows Desktop Runtime 8.0
- Microsoft Windows Desktop Runtime 9.0
Detailed list of February 2026 third-party patches
For a complete list of applications, versions, and the number of remediated vulnerabilities, see the table below generated using Application Workspace data.
| Product Name | Version Name | Vulnerabilities Remediated |
| Brave Browser | 1.87.190 | 3 |
| Brave Browser | 1.86.148 | 2 |
| Brave Browser | 1.87.186 | 11 |
| Brave Browser | 1.87.188 | 1 |
| Burp Suite Community Edition | 2026.2.0 | 11 |
| Burp Suite Community Edition | 2026.2 | 11 |
| Burp Suite Professional Edition | 2026.2.0 | 11 |
| Burp Suite Professional Edition | 2026.2 | 11 |
| Coder | 2.29.5 | 1 |
| Coder | 2.28.10 | 1 |
| Coder | 2.30.0 | 1 |
| Docker Desktop | 4.62.0 | 2 |
| Docker Desktop | 4.62.0.219486 | 2 |
| EnterpriseDB Corporation PostgreSQL 14 | 14.21.1 | 4 |
| EnterpriseDB Corporation PostgreSQL 15 | 15.15.3 | 2 |
| EnterpriseDB Corporation PostgreSQL 15 | 15.16.1 | 4 |
| EnterpriseDB Corporation PostgreSQL 16 | 16.11.3 | 2 |
| EnterpriseDB Corporation PostgreSQL 16 | 16.12.1 | 4 |
| EnterpriseDB Corporation PostgreSQL 17 | 17.7.3 | 2 |
| EnterpriseDB Corporation PostgreSQL 17 | 17.8.1 | 4 |
| EnterpriseDB Corporation PostgreSQL 17 | 17.8 | 4 |
| EnterpriseDB Corporation PostgreSQL 18 | 18.2.1 | 5 |
| EnterpriseDB Corporation PostgreSQL 18 | 18.1.3 | 2 |
| Erlang OTP | 28.3.2.0 | 1 |
| Google Chrome | 144.0.7559.116 | 3 |
| Google Chrome | 145.0.7632.117 | 3 |
| Google Chrome | 145.0.7632.45 | 11 |
| Google Chrome | 145.0.7632.46 | 11 |
| Google Chrome | 144.0.7559.133 | 2 |
| Google Chrome | 144.0.7559.132 | 2 |
| Google Chrome | 144.0.7559.109 | 3 |
| Google Chrome | 145.0.7632.110 | 3 |
| Google Chrome | 145.0.7632.76 | 1 |
| Google Chrome | 144.0.7559.75 | 1 |
| Google Chrome for Business | 145.0.7632.117 | 3 |
| Google Chrome for Business | 145.0.7632.46 | 11 |
| Google Chrome for Business | 144.0.7559.133 | 2 |
| Google Chrome for Business | 145.0.7632.110 | 3 |
| Google Chrome for Business | 145.0.7632.76 | 1 |
| Google Chrome for Education | 145.0.7632.117 | 3 |
| Google Chrome for Education | 145.0.7632.46 | 11 |
| Google Chrome for Education | 144.0.7559.133 | 2 |
| Google Chrome for Education | 145.0.7632.110 | 3 |
| Google Chrome for Education | 145.0.7632.76 | 1 |
| Google Go Programming Language | 1.25.7 | 2 |
| Google Go Programming Language | 1.24.13 | 2 |
| IBM Semeru Runtime Open Edition JDK 11 (LTS) | 11.0.30.7 | 10 |
| IBM Semeru Runtime Open Edition JDK 17 (LTS) | 17.0.18.8 | 10 |
| IBM Semeru Runtime Open Edition JDK 21 | 21.0.10.7 | 10 |
| IBM Semeru Runtime Open Edition JDK 25 | 25.0.2.10 | 10 |
| IBM Semeru Runtime Open Edition JDK 8 (LTS) | 8.0.482.8 | 5 |
| IBM Semeru Runtime Open Edition JRE 11 (LTS) | 11.0.30.7 | 10 |
| IBM Semeru Runtime Open Edition JRE 17 (LTS) | 17.0.18.8 | 10 |
| IBM Semeru Runtime Open Edition JRE 21 | 21.0.10.7 | 10 |
| IBM Semeru Runtime Open Edition JRE 25 | 25.0.2.10 | 10 |
| IBM Semeru Runtime Open Edition JRE 8 (LTS) | 8.0.482.8 | 5 |
| Microsoft .NET Runtime 10.0 | 10.0.3 | 1 |
| Microsoft .NET Runtime 8.0 | 8.0.24 | 1 |
| Microsoft .NET Runtime 8.0 | 8.0.24.35720 | 1 |
| Microsoft .NET Runtime 9.0 | 9.0.13 | 1 |
| Microsoft .NET SDK 10.0 | 10.0.103 | 1 |
| Microsoft .NET SDK 8.0 | 8.4.1826.7203 | 1 |
| Microsoft .NET SDK 8.0 | 8.0.418 | 1 |
| Microsoft .NET SDK 9.0 | 9.0.311 | 1 |
| Microsoft 365 Apps | 2601 (Build 16.0.19628.20204) | 7 |
| Microsoft 365 Apps | 2508 (Build 16.0.19127.20532) | 7 |
| Microsoft 365 Apps | 2512 (Build 16.0.19530.20226) | 7 |
| Microsoft 365 Apps | 2601 (Build 16.0.19628.20166) | 11 |
| Microsoft ASP.NET Core Runtime 10.0 | 10.0.3 | 1 |
| Microsoft ASP.NET Core Runtime 8.0 | 8.0.24.26072 | 1 |
| Microsoft ASP.NET Core Runtime 8.0 | 8.0.24 | 1 |
| Microsoft ASP.NET Core Runtime 9.0 | 9.0.13 | 1 |
| Microsoft ASP.NET Core Runtime Hosting Bundle 10.0 | 10.0.3 | 1 |
| Microsoft ASP.NET Core Runtime Hosting Bundle 8.0 | 8.0.24.26072 | 1 |
| Microsoft ASP.NET Core Runtime Hosting Bundle 9.0 | 9.0.13 | 1 |
| Microsoft Azure CLI | 2.83.0 | 4 |
| Microsoft Edge Beta | 145.0.3800.58 | 11 |
| Microsoft Edge Beta | 145.0.3800.58 | 12 |
| Microsoft Edge Beta | 145.0.3800.58 | 7 |
| Microsoft Edge for Business | 145.0.3800.70 | 3 |
| Microsoft Edge for Business | 145.0.3800.82 | 3 |
| Microsoft Edge for Business | 144.0.3719.115 | 2 |
| Microsoft Edge for Business | 145.0.3800.58 | 7 |
| Microsoft Edge for Business | 145.0.3800.58 | 11 |
| Microsoft Edge for Business | 145.0.3800.58 | 12 |
| Microsoft Project | 2601 (Build 16.0.19628.20204) | 7 |
| Microsoft Visio | 2601 (Build 16.0.19628.20204) | 7 |
| Microsoft Visual Studio 2022 Community | 17.14.36930.0 | 3 |
| Microsoft Visual Studio 2022 Enterprise | 17.12.36929.3 | 1 |
| Microsoft Visual Studio 2022 Enterprise | 17.14.36930.0 | 3 |
| Microsoft Visual Studio 2022 Professional | 17.12.36929.3 | 1 |
| Microsoft Visual Studio 2022 Professional | 17.14.36930.0 | 3 |
| Microsoft Visual Studio Code | 1.109.2 | 2 |
| Microsoft Visual Studio Team Explorer 2022 | 17.14.36930.0 | 3 |
| Microsoft Windows Desktop Runtime 10.0 | 10.0.3 | 1 |
| Microsoft Windows Desktop Runtime 8.0 | 8.0.24.35722 | 1 |
| Microsoft Windows Desktop Runtime 9.0 | 9.0.13 | 1 |
| Mozilla Firefox | 148.0 | 51 |
| Mozilla Firefox | 147.0.4 | 1 |
| Mozilla Firefox ESR 115 | 115.33.0 | 21 |
| Mozilla Firefox ESR 115 | 115.32.1 | 1 |
| Mozilla Firefox ESR 140 | 140.8.0 | 37 |
| Mozilla Firefox ESR 140 | 140.7.1 | 1 |
| Mozilla Thunderbird | 148.0 | 50 |
| Mozilla Thunderbird | 147.0.2 | 1 |
| Mozilla Thunderbird | 148.0 | 100 |
| Mozilla Thunderbird | 148.0 | 40 |
| Mozilla Thunderbird | 147.0.2 | 2 |
| Mozilla Thunderbird ESR 140 | 140.8.0 | 37 |
| Mozilla Thunderbird ESR 140 | 140.8.0 | 74 |
| Mozilla Thunderbird ESR 140 | 140.8.0 | 7 |
| Mozilla Thunderbird ESR 140 | 140.7.2 | 1 |
| Mozilla Thunderbird ESR 140 | 140.7.2 | 2 |
| Node.js 24 | 24.13.1 | 2 |
| Notepad++ | 8.9.2 | 1 |
| pgAdmin 4 | 9.12 | 1 |
| TeamCity | 2025.11.3 | 3 |
| TeamViewer | 15.74.5 | 1 |
| TeamViewer | 15.74.5.0 | 1 |
| TeamViewer Host | 15.74.5 | 1 |
| TeamViewer Host | 15.74.5.0 | 1 |
| TeamViewer QuickSupport | 15.74.5.0 | 1 |
| TurboVNC | 3.3 | 16 |
| VisualSVN Server | 5.4.6 | 13 |
| Vivaldi | 7.8.3925.66 | 1 |
| Vivaldi | 7.8.3925.70 | 3 |
| Waterfox | 6.6.9 | 37 |
| Wireshark | 4.4.14 | 4 |
| Wireshark | 4.6.4 | 3 |
Application management at the speed of your operations
Vulnerabilities move fast, especially in a distributed workforce. Discover how Recast’s application management product, Application Workspace, helps IT teams keep applications patched, compliant, and correctly configured, wherever work happens.


