Around March of this year, Microsoft announced that it would be entering the third-party application patching space with a new product, Microsoft Enterprise App Management. This was a huge announcement, as Microsoft had historically shied away from anything outside of patching their own products. When first announced, they provided very little information and they had remained radio silent since then.
That is until the past few weeks.
At MMS (Midwest Management Summit) Miami this year, Microsoft hosted a session covering Enterprise App Management and gave attendees a few working demos. Even more has come out since then, particularly at Microsoft Ignite.
I was lucky enough to attend one of the sessions at MMS Miami. Here’s what I learned along with my initial reflections.
Why Microsoft Enterprise App Management?
Microsoft began by laying out the values they are trying to embody with Enterprise App Management.
Values
- Streamline app management
- Reduce security risks and vulnerabilities
- Stay current with updates
With third-party application vulnerabilities now causing more breaches than ever, we can all agree that these values align closely with the current challenges and mitigation efforts of most organizations. It also explains well while Microsoft would put new focus on this space.
Now let’s get into what the tool can actually do and when we can expect to use it in the wild.
When is Enterprise App Management Coming?
Currently Enterprise App Management is in private preview. Microsoft gave a public launch date of February 1st, 2024 at MMS Miami. While I am always skeptical when quoted a hard date, the Microsoft employees presenting appeared confident that this date will hold.
What to Expect
In its current state and on the launch date, there will be a total of 40 applications available. This was fewer than I anticipated. Only applications that are publicly available for download will be covered, so no applications behind a login portal will be available initially.
Hopefully the app catalog grows quickly, as I know this will be a sticking point for many large organizations that are dealing with hundreds of applications across their endpoints. For smaller organizations with fewer applications, however, this may be enough to entice them into trialing the product.
Currently only Windows will be supported. There were questions surrounding support for Mac in the session I attended. It makes sense that people would be interested in Mac, as Intune has become the supported platform for managing Macs since support for MacOS was removed from ConfigMgr. For those who manage Macs via Intune, they will have to wait or find another tool to keep third-party applications updated on those devices, which may be a sticking point for some.
How about Adding Applications into the Environment?
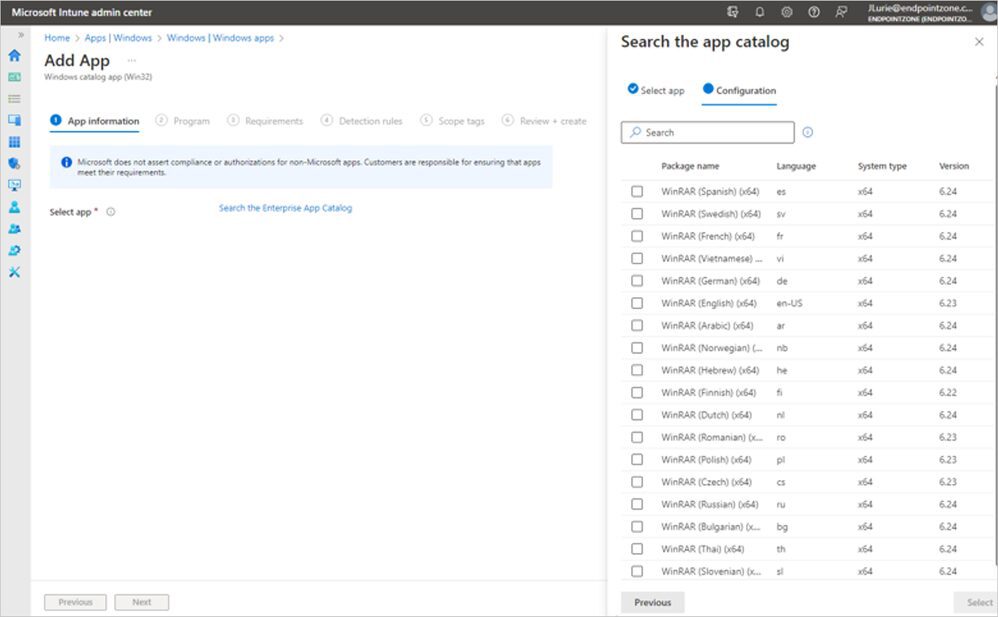
As far as the process of adding an application, it seemed pretty straightforward. You can add an application via their application catalog. During this process, a 6-page wizard will guide you through the process of adding the application. You will have to fill out fields on these pages. Common switches for these applications will be supported (think silent install flag), but not all.
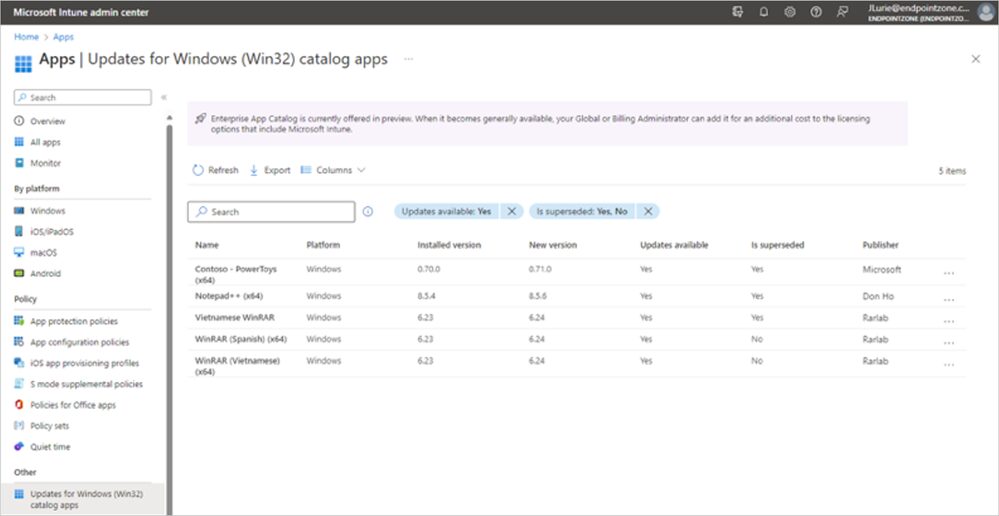
When a new update comes out for an application in your environment, it will be available via the Updates for Windows Catalog Apps page. From there you can deploy the newest version. You will again work through a progression of pages to update. This is currently a manual process. I hope and anticipate that Microsoft will increase the automation within the app.
My Initial Thoughts: Microsoft Enterprise App Management
So how did I leave this session feeling? It’s a solid first step for Microsoft. “But Kody, you guys sell a competing product in Application Manager!” I know, I know. However, this really didn’t play into my initial reaction.
My main reactions centered around a couple key factors. First, the product catalog currently sits at 40 applications. I expect this is a starting point for Microsoft and therefore I look forward to seeing them expand the catalog of supported apps.
Secondly, the user experience currently requires manual management of the update process. I am sure many early adopters will be pushing for automations to be built into the application.
The Competition
Considering the number of players in the third-party patching space, I expect Microsoft’s first foray into the third-party patching space will catch the attention of all key players. Competition, at its best, breeds innovation. I’m hopeful this increased competition will encourage all—Microsoft, Recast Software, and others—to up their game to the benefit of the end users. Microsoft’s entrance can ideally serve as motivation for new features and innovations within the third-party patching space.
Conclusion: Microsoft Enterprise App Management
This product will be a great starting point for many organizations. As a former SysAdmin for a small organization that managed endpoints through Intune, I can see this serving those organizations well. Unfortunately, my previous employer took the blind eye approach to keeping third-party applications updated, and I know many other organizations are in the same boat. This tool will help to fill that gap for a handful of well-used applications.
Additionally, Microsoft will lower the barrier to entry for many because it will be tacked onto Microsoft licensing, which can be easier to clear in budgets for many organizations. We all know the struggle of getting approval for new tools.
Finally, if even a few organizations start actually patching third-party applications that they were previously ignoring, this would be significant win. Too many organizations are currently leaving these applications to either auto-update or sit at their current version, which leaves these organizations unnecessarily vulnerable.
