Systems Management
Building a ConfigMgr Lab from Scratch: Step 13 – Cloud Management Gateway (CMG) – Certs PreReq
Topics: Systems Management
Building a ConfigMgr Lab from Scratch: Step 13
Cloud Management Gateway (CMG) – Certs PreReq
Hey, so I’m going back to working on my lab, and now I’m adding a Cloud Management Gateway (CMG). If you followed along, you’ll be all set for where I pick up.
Assumptions: you’ve got an Internal Enterprise CA setup, and you’ll use your Internal CA to support CMG and the required Certs needed.
See the Certificate Authority Post to help setup your CA if you haven’t done that yet.
I’ll also mention this is NOT the only way to setup CMG, you can do it without an Internal CA, and use a certificate from a 3rd party Certificate Authority, but I’m not going to cover that here.
Recommended reading and viewing:
- MS Docs: Set up cloud management gateway for Configuration Manager
- Youtube: Cloud Management Gateway – ConfigMgr CB and the Microsoft cloud platform (Steve Rachui @steverac)
- Youtube: How To Setup Cloud Management Gateway (CMG) in Microsoft SCCM (Justin Chalfant @SetupConfigMgr)
Full disclosure, those are the three items I used to setup CMG, and I highly recommend them. So why continue? MS Docs are good, but I’m a visual guy and like to see the images. The Videos are great, but then you’ve got to get good at pausing videos and working through it. It’s just a matter of personal preference. I give credit to those three items for educating me to be able to create this content.
With that intro behind, let’s layout how we’re going to go through this:
- Create the Required Certificated needed (Lower in this This Post)
- Ensure Workstations are getting their Client Certificates [Lab Setup Post 14]
- Talk Pre-Reqs for Azure Portal
- Setup the Azure Connection in CM Console
- Confirm Connection in Azure Portal
- Start the CMG Setup in CM
- Confirm CMG setup in Azure
With that outline, let’s get started.
Create the Required Certificates needed
So, what Certificates are needed? [MS Docs]
- Client Authentication Certs (on each of the client machines) [MS Docs]
- Web Cert for CMG device. [MS Docs]
- Root CA Cert
Client Auth Cert:
So hopefully you setup your CA, set the Client Auth Cert to Auto Enroll and all of your clients have the cert. For a good walk through, Justin has that on Video too: [YouTube @ 9:26]
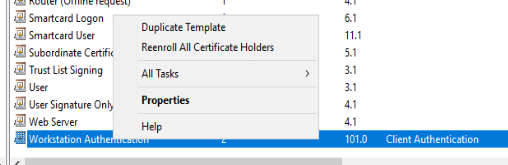
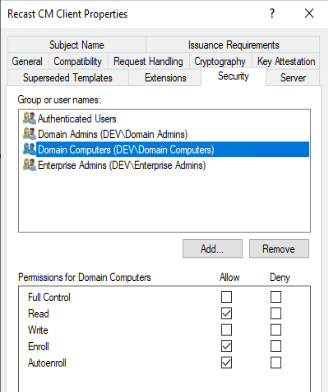
You create a Duplicate of Workstation Cert, Name it what you want, then add Domain Computers to have Read, Enroll and Autoenroll security rights.
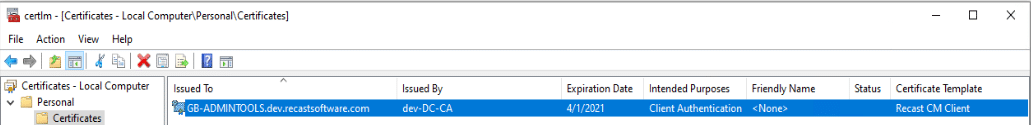
On the workstations, they auto-enroll and will get this after the next policy update:
Web Cert for CMG device:
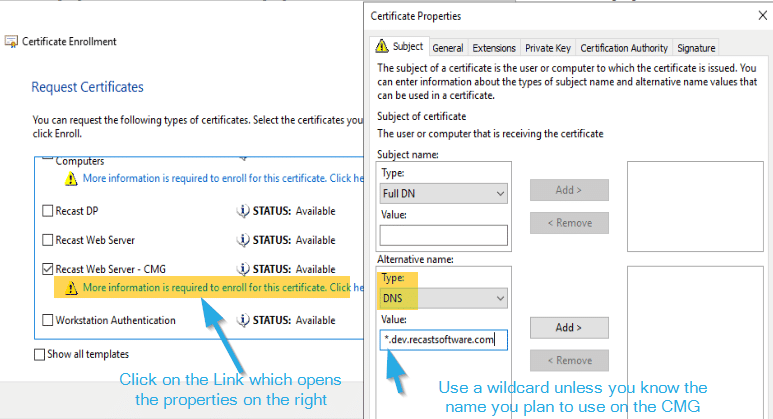
Here you’ll make a duplicate of the Web Server Certificate, and setup a few things. Justin’s video does good job of explaining this too.
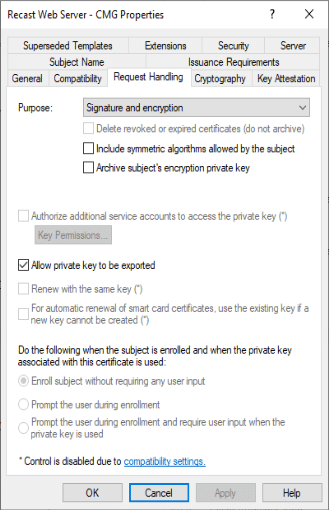
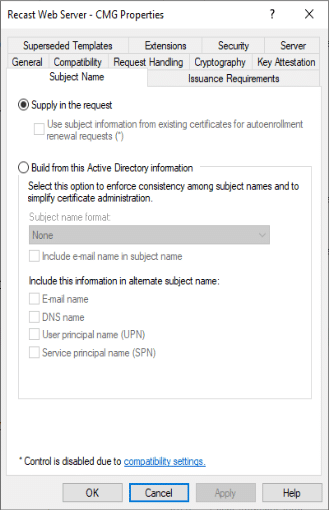
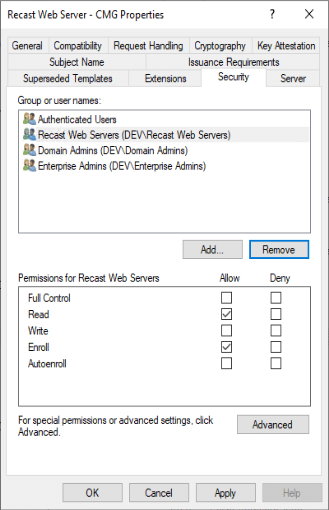
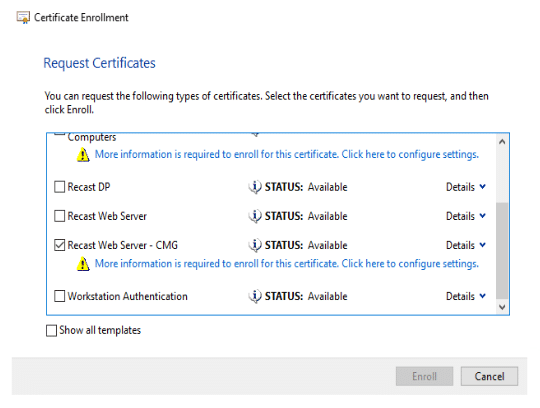
Here I’ve got it set to a group of servers, so I can enroll from any of those to create the cert to export. Now on one of my webservers, I can request the cert:
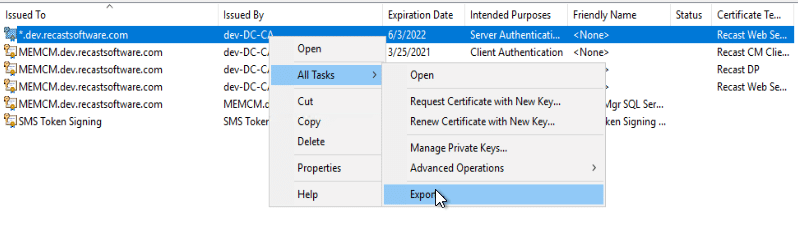
Now that we have it, we need to export it
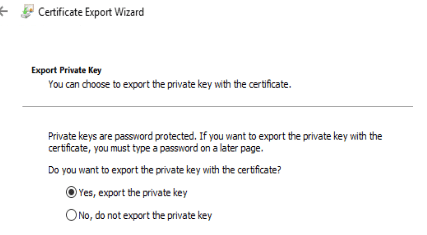
Yes, export that private key!
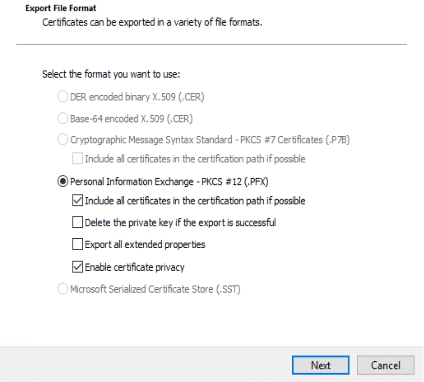
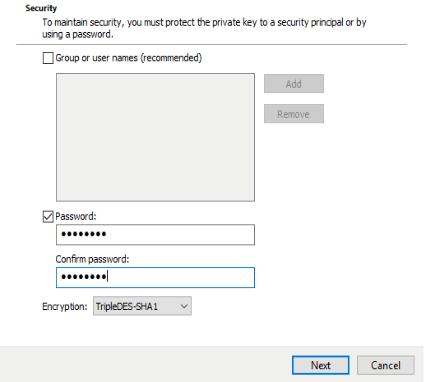
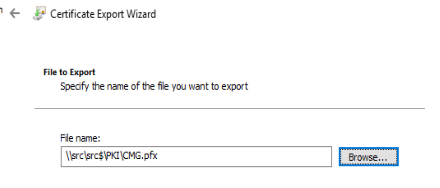
Now then, save the cert pfx file for use when we setup the CMG stuff.
Root CA Export:
While there are several ways to get this, this is how I did it, since I was already here:
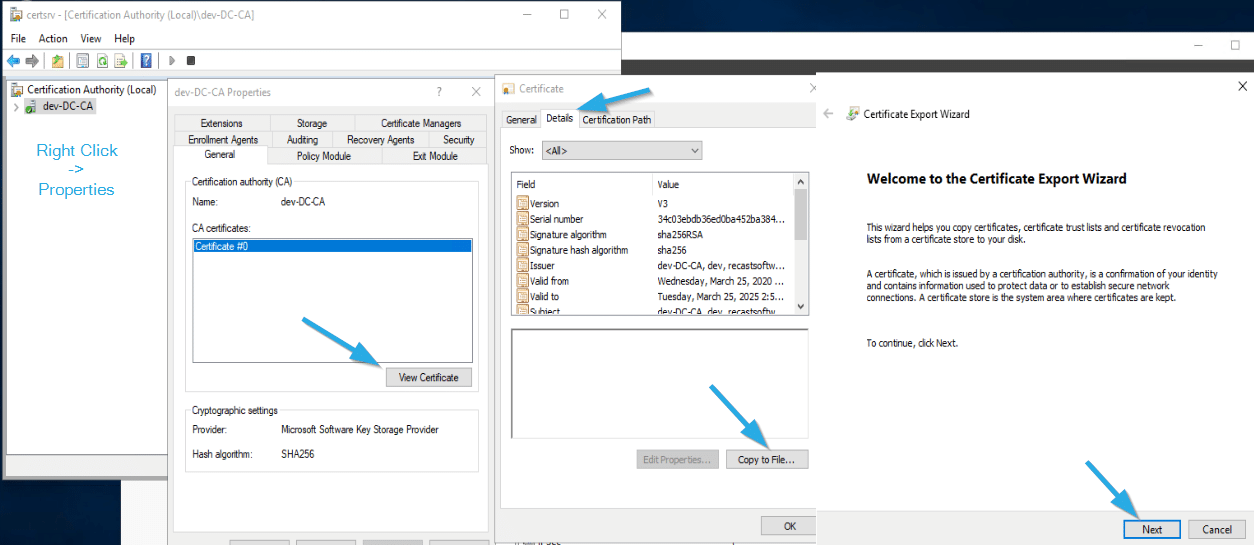
Certificate Authority Console -> Right Click on Server -> Properties -> General -> View Certificate -> Details -> Copy to file… -> Next
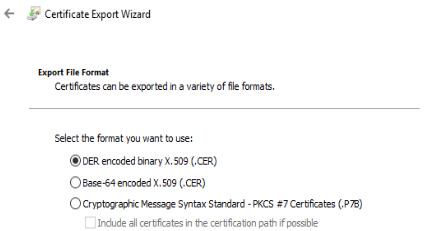
DER (.CER) is what we need.
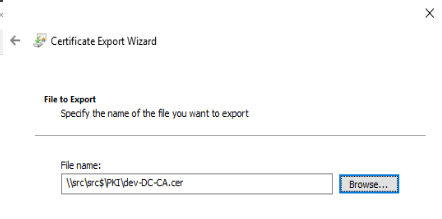
Then Save it to a location.
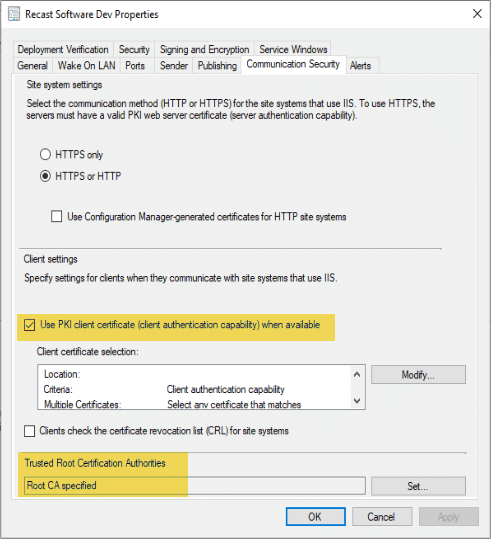
One more thing we’ll want to do in CM is allow CM to use the PKI cert. [MS Docs]
Administration Node -> Site Configuration -> Sites -> Properties -> Communication Security Tab
This cert and others will be used in other places, but this is getting long enough for now. Stick around for the next post.
Building a ConfigMgr Lab from Scratch Series
Series Introduction – Building a CM Lab from Scratch
- Setting up your Domain Controller
- Creating a Router for your Lab using Windows Server
- Certificate Authority – On Domain Controller [Optional]
- ConfigMgr Server Pre-Reqs (Windows Features)
- Configuration Settings (AD & GPOs)
- Source Server (File Share)
- ConfigMgr SQL Install
- ConfigMgr Install
- ConfigMgr Basic Settings
- ConfigMgr Collections & App Deployment
- ConfigMgr OSD
- ConfigMgr Reporting Services
- Cloud Management Gateway (CMG) – Certs PreReq – You are Here
- Cloud Management Gateway (CMG) – Azure Subscription
- Azure Services Connection
- Setting up CMG in the Console
- Cloud Management Gateway (CMG) – Post CMG Config
- Cloud Management Gateway – Client CMG Endpoints