Four Files You Need to Remove from ConfigMgr Environment (Baseline)
In my last blog post, I talked about a presentation that Dana Epp gave on how hackers can gain access to your environment through four different files. Configuration Manager Administrators, though, can make access difficult for these outside threats by removing these files.
Dana recommends that you delete four specific files because they contain crucial passwords that enable hackers to gain a toe-hold in your environment:
- C:sysprep.inf
- C:sysprepsysprep.xml
- %windir%PantherUnattendUnattend.xml
- %windir%PantherUnattend.xml
I will encourage all of my clients to follow his advice, and I agreed to help Dana get the word out by writing this blog post series.
Adding Four Files to Remove to the Configuration Baseline
This process involves a number of steps, and this is the second part of my 5-part series. Now that a Configuration Item exists for each of the four files (see the previous post), let’s add them to a Configuration Baseline.
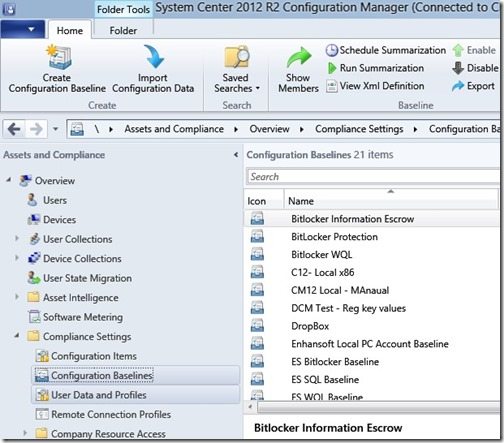
1. In the ConfigMgr 2012 Console, go to Assets and Compliance | Overview | Compliance Settings | Configuration Baselines, and click Create Configuration Baseline in the toolbar.
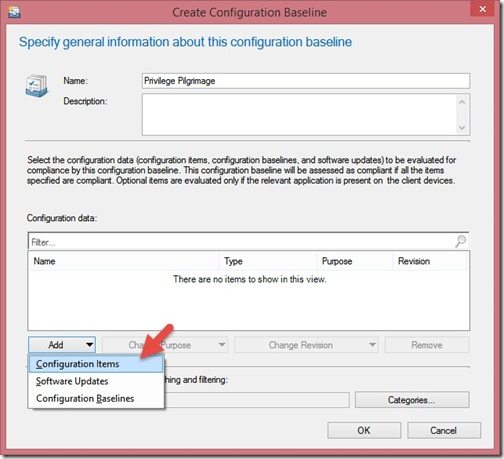
2. Give your Configuration Baseline a name, click Add, and then select Configuration Items.
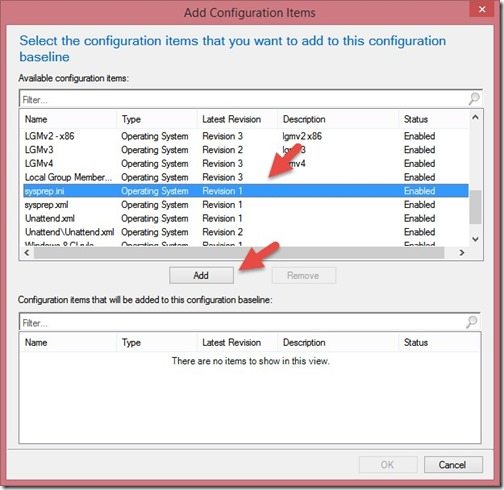
3. Highlight one of the Configuration Items you recently created and click Add.
Repeat this step for the three remaining Configuration Items. (This is the name I asked you to remember in yesterday’s post.)
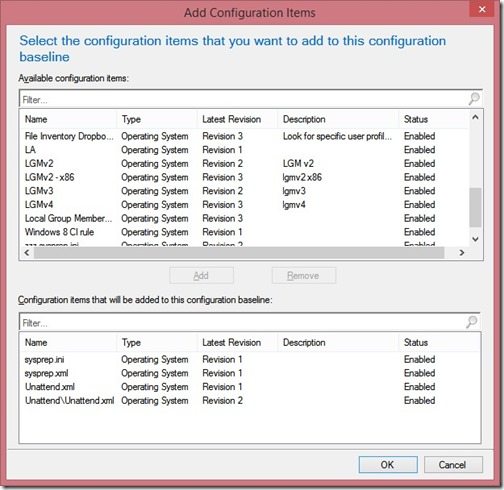
4. Click OK to complete the Configuration Baseline.
In next week’s blog post, I will show you how to deploy the Configuration Baseline to a collection.


